Login Page Phishing Protection
Background
Threat actors often mimic Microsoft 365 authentication pages as part of phishing campaigns to trick users into revealing their login credentials.How threat actors trick users?
Here’s a general overview of how this process works: Creating a Fake Website: The threat actor creates a website resembling the Microsoft 365 login page. They copy the actual page’s design, layout, and branding to make the fake site appear legitimate. Setting Up a Phishing Email: The threat actor sends a phishing email to the target. This email typically contains a call to action that prompts users to log in to their Microsoft 365 account. For example, the email might claim that the user needs to verify their account or check for suspicious activity. Redirecting to the Fake Website: The email contains a link that, when clicked, redirects the user to the fake Microsoft 365 login page created by the threat actor. Capturing Login Credentials: The threat actor captures this information when the user enters their login credentials on the fake site. They can then use these credentials to gain unauthorised access to the user’s Microsoft 365 account. Adversary in the Middle (AitM) Attack: In some sophisticated attacks, threat actors use an AitM proxy like Evilginx. This proxy sits between the user and the legitimate site, capturing login credentials as the user attempts to log in.New ! Login Page Phishing Protection
Login Page Phishing Protection helps your users detect fake login pages. It is based on the original research from https://zolder.io/using-honeytokens-to-detect-aitm-phishing-attacks-on-your-microsoft-365-tenant/, and provides an additional layer of security by leveraging existing features in a novel way to detect and prevent phishing attacks. It’s a clever use of the custom CSS feature in M365 to enhance security.What your users will see
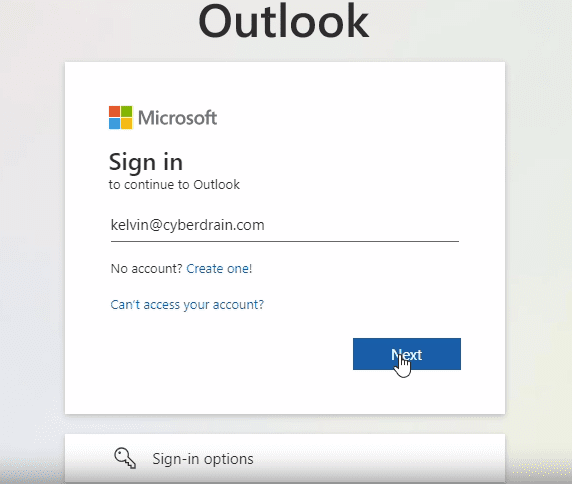
1. Fake Page is presented to the user to sign in.
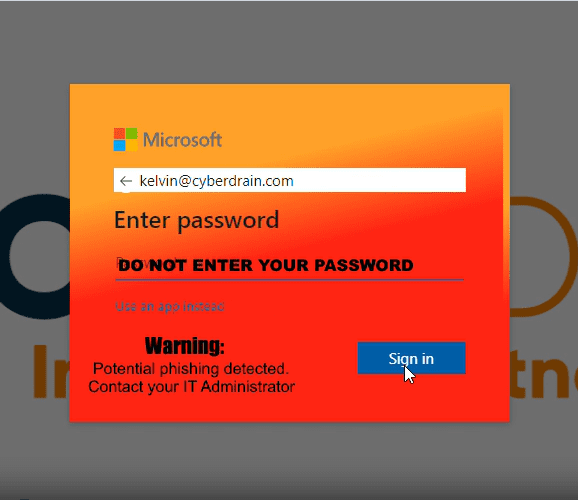
2. The Automated Phishing Protection System detects that the referrer-header is not login.microsoftonline.com and updates the branding with a warning.